The rise of cyber warfare has become a major concern in today’s digital world. With the advancement of technology, cyber attacks are becoming more sophisticated and widespread. Understanding the technology behind these attacks is crucial in order to defend against them effectively.
The Evolution of Cyber Warfare
 Advanced Health Smartwatch for Women Men with Real-Time Monitoring of Heart rate
Advanced Health Smartwatch for Women Men with Real-Time Monitoring of Heart rate
Cyber warfare has evolved significantly over the years. What started as simple hacking attempts has now transformed into complex and coordinated attacks carried out by state-sponsored groups and cybercriminal organizations.
Types of Cyber Attacks
There are various types of cyber attacks, including malware, phishing, ransomware, DDoS attacks, and more. Each of these attacks exploits different vulnerabilities in computer systems and networks.
Tools and Techniques
Cyber attackers use a variety of tools and techniques to carry out their attacks. These can include malware, social engineering, zero-day exploits, and more. Understanding how these tools work is crucial in defending against them.
Cyber Warfare Tactics
Cyber warfare tactics involve the use of technology to disrupt, damage, or gain unauthorized access to computer systems and networks. These tactics can have significant impacts on individuals, organizations, and even entire countries.
The Role of Technology
 Lenovo IdeaPad Slim 5 | 14 inch WUXGA Laptop | Intel Core i7-13620H | 24 GB RAM | 1 TB SSD | Windows 11 Home | Cosmic Blue
Lenovo IdeaPad Slim 5 | 14 inch WUXGA Laptop | Intel Core i7-13620H | 24 GB RAM | 1 TB SSD | Windows 11 Home | Cosmic Blue
Technology plays a significant role in cyber warfare. Advancements in artificial intelligence, machine learning, and encryption have made it easier for cyber attackers to carry out their attacks. However, these same technologies can also be used to defend against cyber threats.
Cyber Security Measures
Implementing robust cyber security measures is essential in protecting against cyber attacks. This can include installing firewalls, using antivirus software, conducting regular security audits, and training employees on best practices for cyber security.
Collaboration and Information Sharing
Collaborating with other organizations and sharing information about cyber threats can help to enhance overall cyber security. By working together, we can better understand the tactics used by cyber attackers and develop more effective defense strategies.
Conclusion
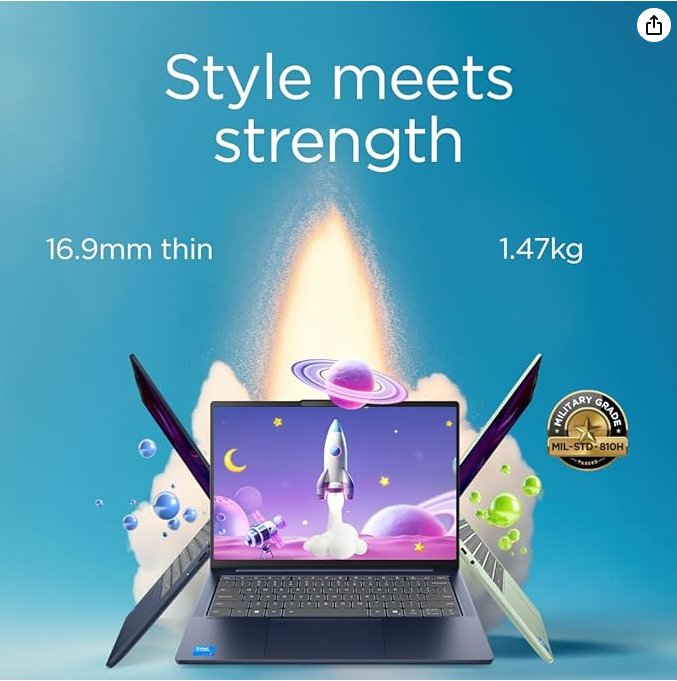 Lenovo IdeaPad Slim 5 | 14 inch WUXGA Laptop | Intel Core i7-13620H | 24 GB RAM | 1 TB SSD | Windows 11 Home | Cosmic Blue
Lenovo IdeaPad Slim 5 | 14 inch WUXGA Laptop | Intel Core i7-13620H | 24 GB RAM | 1 TB SSD | Windows 11 Home | Cosmic Blue
As the threat of cyber warfare continues to grow, it is imperative that we understand the technology behind these attacks and take proactive steps to defend against them. By staying informed and implementing robust cyber security measures, we can better protect ourselves and our digital assets from cyber threats.